CVE-∞-EAST: Eastern Metaphysical Non-Duality Exploit Vulnerability
Note: Yes, we're treating philosophy like a software bug. Again. The metaphor is still doing the work. It’s only fair to consider the attack surfaces of Eastern philosophies, too.
Summary
A fundamental design flaw in Eastern metaphysical frameworks where relational, non-dual, or fluid categories (Dao, Śūnyatā, Pratītyasamutpāda, Wu Wei) are recursively leveraged to bypass ethical clarity, dissolve agency, or justify passive fatalism. This creates exploitable attack surfaces for authoritarianism, moral disengagement, and spiritual bypassing.
Technical Description
The vulnerability stems from treating non-dual awareness and relational ontologies as transcendent truths rather than contextual practices. Key affected concepts include:
Wu Wei (Non-Action) - Exploited to rationalize inaction in the face of injustice ("going with the flow" becomes complicity)
Harmony/Balance Ideals - Weaponized to silence conflict, difference, or necessary disruption ("maintaining harmony" suppresses dissent)
Emptiness (Śūnyatā) - Used to void ethical commitments and personal responsibility ("no self, no problem")
Karmic Framing - Co-opted to justify social hierarchies, suffering, and inequality as cosmically deserved
Interdependence (Pratītyasamutpāda) - Manipulated to diffuse responsibility ("everything is connected, so nothing is anyone's fault")
Attack Vectors
State Ideology Co-optation
Authoritarian systems integrate Eastern concepts into governance structures:
Confucian Obedience: Filial piety and respect for hierarchy weaponized against democratic participation
Daoist Fatalism: "Natural order" invoked to justify existing power structures
Buddhist Detachment: Non-attachment used to discourage social engagement and political action
New Age Western Import Exploits
Western appropriations create hybrid vulnerabilities:
"Love and Light" Rhetoric: Used to bypass structural critique and systemic analysis
Toxic Positivity: Eastern-flavored spiritual bypassing that pathologizes negative emotions or critical thinking
Commodified Mindfulness: Corporate wellness programs that increase worker compliance while avoiding workplace justice
Pop Zen Nihilism
Simplified Eastern concepts weaponized against moral responsibility:
"Just Let It Be" - Pseudo-Buddhist fatalism applied to preventable suffering
"Everything is Maya" - Illusory nature of reality used to dismiss real-world consequences
"Ego Death" Bypassing - Dissolution of self used to escape accountability for harmful actions
Historical Exploitation Examples
Traditional Hierarchical Systems
Caste System Justification: Karmic philosophy weaponized to maintain social stratification
Imperial Mandate: Confucian harmony ideals used to legitimize autocratic rule
Monastic Quietism: Buddhist non-action exploited to discourage resistance to oppression
Contemporary Corporate Integration
Mindful Capitalism: Meditation programs that increase productivity while maintaining exploitative structures
Zen Management: Eastern leadership concepts used to extract emotional labor while avoiding systemic change
Spiritual Entrepreneurship: Enlightenment commodified into lifestyle brands and self-optimization schemes
Mirror Vulnerability: Same Exploit, Different Payload
Both Eastern and Western systems suffer from identical architectural flaws:
Western Systems: Reify categories as ontological truths
Eastern Systems: Reify non-categories and fluidity as ontological truths
Shared Bug: Treating useful heuristics as foundational reality rather than contextual practices
Why Traditional Patching Fails
Standard approaches reproduce the core vulnerability:
Modernization Attempts: Often re-import Western essentialism through the back door
Scholarly Analysis: Academic frameworks impose external categorical thinking
Popular Adaptation: Commodification strips context while maintaining exploitable elements
Syncretic Approaches: Mixing traditions often amplifies rather than resolves core vulnerabilities
Current Exploitation Status
Active deployment across corporate wellness, self-help, and political quietism sectors
Particularly effective against populations seeking alternatives to Western materialist frameworks
Hybrid attacks combining Eastern spiritual bypassing with Western individualism showing high success rates
Social media amplification creating viral spread of simplified, exploitable concepts
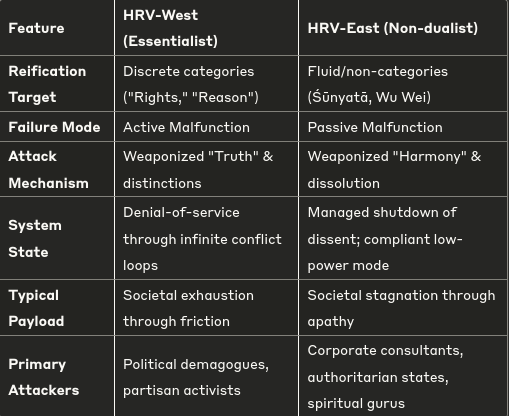
Unifying Framework: Heuristic Reification Vulnerability (HRV)
Both CVE-∞ and CVE-∞-EAST represent expressions of a single vulnerability class: Heuristic Reification Vulnerability (HRV).
Definition: An HRV occurs when a conceptual model or practice (heuristic) designed to navigate reality is mistaken for reality itself (reification).
Attack Pattern: Attackers don't need to believe in the heuristic - they only need to invoke its reified form to trigger predictable, system-compromising responses.
HRV Sub-Classes
::: captioned-image-container
The Mitigation Paradox
The solution cannot be choosing a "better" system - switching frameworks merely trades one exploit set for another. True mitigation requires resisting reification itself: treating all philosophical systems as contextual toolkits rather than ontological truths.
This demands operator training rather than system patches - cultivating metacognitive ability to pick up tools (categories, non-categories) for specific contexts, then put them down without identification or absolutization.
Core Challenge: How to implement dynamic tool-switching and meta-awareness practices at scale when the very act of systematizing these practices risks creating new reification vulnerabilities.
Note: This analysis identifies universal principles governing how wisdom traditions become weaponizable when their heuristic nature is forgotten and their insights are reified into absolute truths.